Security Review: Amazon Kindle
With rumors of Amazon revealing their next Kindle on Monday (an honor Engadget, along with other blogs has already done for them), and as a user of the first Kindle, I figured that with its numerous features, communication methods, and potential appeal, it was an appropriate time to do a security review of the system. And as an irrelevant aside, I think the new model is really ugly.
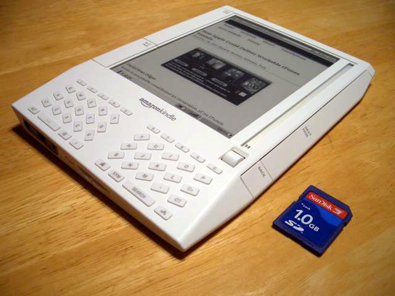
The Kindle is an e-book reader, one of two primary contenders in the market at this point in time (the other being the Sony Reader). Like its competition, it features an E-paper screen, which is ideal for this application due to the fact that it requires no harsh backlight, and requires no power to maintain image – only to change image. In addition to being able to store and display ebooks (in unsecured Mobipocket, plain text, or proprietary Amazon format), the Kindle’s most fascinating feature is its EVDO antenna. Through Sprint, the Kindle provides free data transfer. The primary function here is to provide access to a wireless Amazon store from which users can purchase and download DRM-secured ebooks, but there is also a primitive web browser in the software.
Assets & Security Goals:
- Preventing users from stealing books is the primary business security concern for Amazon. There is a twofold issue here: there is the potential for users to snoop in on the wireless transmission of the book itself, but there is also the potential of a user to steal the book once it is on the device – hence, there needs to be both wireless security and DRM on the final file.
- Protecting the privacy of the user is a concern for the users of the device – while there aren’t any explicit laws protecting people’s reading history as there are for television and movies, what a person is reading on the device should still remain private to that user.
- Providing security for the user while they browse the web is another concern that involves specifically the consumer rather than Amazon – this should be a simple matter of implementing existing security standards for the web.
Adversaries & Threats
- People who would like to pirate content are again the primary thread to Amazon’s business on the Kindle. Protecting the ebook files in transit and storage should stop them from stealing Amazon ebooks, though given the Kindle’s capability of reading generic unsecured Mobipocket files, people could just as easily pirate those and drop them on the device over USB.
- People who would like to steal users’ information are easier to defend against. They may want to steal credit card information as transactions occur, or find out what a user is reading. If the victim has sensitive material, such as corporate documents and manuals, or manuscripts for unpublished books, these may be a target.
- People who want to cause hard to the user, either by purchasing books on their device without permission, or cause them to lose the books they currently have. These people don’t have as much work to do as the previous, as it is easier to cause harm than it is to steal information.
Potential weaknesses
- Theft – should an attacker gain physical control over the device, there is virtually nothing that could be done to stop him/her from purchasing items on the tab of the actual user, accessing any pages with the web browser that may have saved passwords or cookies, and learning what the user has been reading – including reading sensitive material as described earlier.
- The display is perhaps a surprising point of attack. However, as a user of the first Kindle, I have noticed that at times when the unit shuts off and blanks its screen, a trace amount of ink is left visible, enough so that display text is still visible. Given that the display works on the principle of magnetically charging droplets of ink, it might be that with magnetically sensitive instruments it would be possible to learn even more of what a display has shown. Given that sensitive documents or manuscripts may have been read on the device prior to its shutoff, and especially that it contains a web browser which could be used to browse sensitive material such as bank accounts, not to mention that passwords are inputted similarly to cell phones – with the last character inputted remaining visible until the next is typed – this could be a serious attack vector if enough study is put into the physics of the display.
- The obvious vector of breaking whatever security is on the DRM’d files (after all, the method and key for decrypting them must be on the device somewhere if it’s able to display the books) would be an easy approach to breaking the security of the platform in general. Attacking the wireless transmission itself would likely be much more difficult since it’s probably based on well-established cryptographic algorithms, but breaking DRM is certainly not without a very large precedent.
Potential defenses
- Passwords more prominently used throughout the device would mitigate the theft concern almost entirely (assuming, of course, chosen passwords are secure). Were the device to require passwords to power on or access certain user-determined books on the device depending on their sensitivity (the latter using encryption on the file rather than just an operating system refusal to open the file given that it could be retrieved by USB), much of the concern of the device falling into an adversary’s hands is mitigated. Potentially along with a remote kill-switch like that implemented on enterprise cell phones, the threat of the device being stolen would be greatly reduced.
- More screen blanking would help the display issue greatly – at least with the immediate and definite problem of trace ink. The device typically flashes the entire screen to black and then white to clear the screen, and I’m assuming that a few more rounds of this would reduce the amount of material left on-screen afterwards. Since the rest of the threat is primarily speculation on my part, I’m not sure as to what the defense would be.
- The ability to update the DRM of files remotely could be one way that Amazon could use to secure the files. It’s security by obscurity, but constantly changing the DRM scheme could be one way of preventing the attack from figuring out how to crack the protected books. I’m not skilled enough in cryptography to know if there’s a way the device could possibly secure the books given that the decryption method and key are both stored on the device itself, without external authentication (the EVDO antenna may be turned off, and DRM’d files are still accessible in remote regions).
Most of my analysis is based on what Amazon wishes the Kindle would be – a general purpose reading device integral to the lives of those who use it – rather than what it is now – a largely novelty gadget which, while well-executed, is too expensive to be a reasonable purchase for all but the most fanatic book fans and extreme road warriors. Scenarios such as heavy duty web browsing (unlikely due to the slow response of the screen and slow transfer over EVDO), storage of anything other than books (such as the confidential material I listed above), and other such ubiquitous uses of the device are not a reality at this point.
However, if Amazon is serious about the device becoming hugely successful in the future, they are all issues that must be addressed soon.